Obiettivi | Certificazione | Contenuti | Tipologia | Prerequisiti | Durata e Frequenza | Docenti | Modalità di Iscrizione | Calendario

Il Corso Cisco CCNA Cybersecurity – CBROPS Understanding Cisco Cybersecurity Operations Fundamentals fornisce ai Partecipanti una preparazione tecnica solida sulle attività fondamentali di un moderno Security Operations Center (SOC), con focus su security concepts, security monitoring, host-based analysis, network intrusion analysis e security policies and procedures. Il percorso affronta il funzionamento operativo di un SOC di primo livello, l’uso di SOC metrics, i flussi di lavoro supportati da workflow management e automation, e l’analisi di eventi e incidenti attraverso log, telemetria e strumenti di detection. Vengono trattate tecnologie e ambiti chiave come Windows e Linux, endpoint security, SIEM, SOAR, log management, NetFlow, TCP dump, NGFW, stateful firewall, application visibility and control, web/email content filtering, PKI, X.509 certificates, Wireshark, IDS/IPS, proxy logs, full packet capture, sandbox e malware analysis tools. Il corso approfondisce inoltre TCP/IP attacks, DoS/DDoS, MITM, SQL injection, command injection, cross-site scripting, social engineering, C2, ransomware, tecniche di evasion/obfuscation, nonché modelli come Cyber Kill Chain e Diamond Model of Intrusion. Ampio spazio è dedicato anche a cloud security, identity and access management, data protection, continuous monitoring, incident response, CSIRT e ai framework NIST SP 800-61 e NIST SP 800-86. Il corso contribuisce alla preparazione dell’esame di Certificazione Cisco CCNA CCNACBR – Esame 200-201.
Sintesi Statistica:
- Corsi realizzati: 93;
- Numero Corsisti: 796;
- Superamento Esame: 88,35%
Contattaci ora per ricevere tutti i dettagli e per richiedere, senza alcun impegno, di parlare direttamente con uno dei nostri Docenti (Clicca qui)
oppure chiamaci subito al nostro Numero Verde (800-177596).
Calling from abroad? Reach us at +39 02 87168254.
Obiettivi del corso
Di seguito una sintesi degli obiettivi principali del Corso Corso CCNA Cybersecurity – CBROPS Understanding Cisco Cybersecurity Operations Fundamentals:
- Comprendere il funzionamento di un SOC, l’uso di SOC metrics, workflow automation e processi operativi di security monitoring.
- Analizzare endpoint, Windows, Linux e tecnologie di host-based security come HIDS, antimalware e host-based firewall.
- Interpretare telemetria e dati di rete tramite NetFlow, TCP dump, full packet capture, NGFW, IDS/IPS e Wireshark.
- Riconoscere attack vectors, malicious activity, TCP/IP attacks, web application attacks, malware, C2 e pattern di comportamento sospetto.
- Applicare pratiche di incident investigation, event correlation, playbook execution, incident response e controlli di cloud security e data protection.
Certificazione del corso
Esame 200-201 CCNACBR – CCNA Cybersecurity Certification;
La certificazione CCNA Cybersecurity valuta se il candidato possiede le conoscenze e le competenze richieste per operare nei domini fondamentali della cybersecurity operations, ed è l’esame associato alla certificazione CCNA Cybersecurity. Il superamento dell’esame consente quindi di ottenere la relativa certificazione. I contenuti testati coprono innanzitutto i Security Concepts, inclusi CIA triad, defense-in-depth, risk, threat, vulnerability, exploit, modelli di access control, CVSS, threat intelligence, threat hunting, malware analysis, threat modeling, DevSecOps, oltre a temi come SIEM, SOAR, log management, ambienti container, virtual environments e cloud security deployments. L’esame verifica inoltre la capacità dell’esaminato di interpretare attività di Security Monitoring e Host-Based Analysis, comprendendo sorgenti dati e tecnologie come TCP dump, NetFlow, next-gen firewall, stateful firewall, application visibility and control, web/email content filtering, full packet capture, metadata, alert data, nonché l’analisi di sistemi Windows e Linux, host-based intrusion detection, antimalware, antivirus, host-based firewall, log di sistema e output di sandbox o strumenti di malware analysis. Una parte centrale riguarda la Network Intrusion Analysis, con verifica su IDS/IPS, proxy logs, NetFlow, PCAP, Wireshark, deep packet inspection, packet filtering, protocolli come IPv4, IPv6, TCP, UDP, ICMP, DNS, HTTP/HTTPS, e sull’identificazione di artifact quali IP address, ports, hashes, URI/URL e API calls. Sono inclusi anche DoS/DDoS, MITM, SQL injection, command injection, cross-site scripting, social engineering, C2, ransomware ed evasion techniques. Infine, l’esame misura la conoscenza di Security Policies and Procedures, con focus su incident response, NIST SP 800-61, NIST SP 800-86, evidence handling, data preservation, network/server profiling, protezione di PII, PSI, PHI, e classificazione degli eventi tramite Cyber Kill Chain Model e Diamond Model of Intrusion.
Contenuti del corso
Security Operations Center
- Introduction to SOC Operations
- Defining the Security Operations Center
- Types of Security Operations Centers
- SOC analyst functions, tools and operational workflows
- Data analytics for security operations
- Hybrid environments, automated reporting and anomaly alerting
- Roles and responsibilities in a Security Operations Center
- Staffing an effective incident response team
- Developing key relationships with internal and external resources
- SOC metrics, detection effectiveness and time to detection
- SOC workflow, workflow management systems and automation models
Endpoint Security
- Understanding Windows Operating System Basics
- Windows architecture, processes, services, registry, CLI, PowerShell, networking and administration tools
- Understanding Linux Operating System Basics
- Linux architecture, file system, permissions, shell, processes, services, networking, package management and remote access
- Understanding Endpoint Security Technologies
- Host-based firewall, antivirus, antimalware, HIPS/HIDS, application control, sandboxing and file integrity checking
- Endpoint visibility, host telemetry and endpoint-based detection use cases
Network Security
- Understanding Network Infrastructure and Network Security Monitoring Tools
- NAT fundamentals, ACLs, packet filtering, AAA, access control models and load balancing
- Network-based malware protection and network security monitoring tools
- Understanding Common TCP/IP Attacks
- ARP, IP, ICMP, TCP and UDP vulnerabilities
- Attack surface, attack vectors, reconnaissance, access attacks and spoofing
- Man-in-the-Middle, DoS, DDoS, reflection and amplification attacks
- DHCP attacks, tunneling, proxies, encapsulation and common evasion techniques
Data Security
- Exploring Data Type Categories
- Network security monitoring data and data types
- Full packet capture, packet capture using tcpdump, session data, transaction data, statistical data, metadata and alert data
- Correlating NSM data across multiple sources
- CIA triad, PII, regulatory compliance and intellectual property
- Understanding Basic Cryptography Concepts
- Hashing, encryption, cryptanalysis, symmetric and asymmetric algorithms
- Diffie-Hellman, digital signatures, PKI, certificates, cipher suites, key management, SSH and SSL/TLS
Cloud Security
- Introduction to Cloud Security Fundamentals
- Cloud deployment models and service models
- Shared responsibility model
- Identity and Access Management in cloud environments
- Cloud compliance frameworks and governance controls
- Data protection in cloud workloads
- Secure application deployment principles
- Continuous monitoring and cloud visibility
- Network security controls for cloud environments
- Secure cloud deployments, resilience and disaster recovery strategies
Threat Analysis
- Understanding Incident Analysis in a Threat-Centric SOC
- Cyber Kill Chain and Diamond Model
- MITRE ATT&CK framework and adversary methodology
- Identifying Common Attack Vectors
- DNS, HTTP/HTTPS, HTTP/2, SMTP, SQL and web scripting abuse
- Shellcode, exploits, payload techniques, directory traversal, SQL injection and Cross-Site Scripting
- DNS tunneling, pivoting and browser-based attack techniques
- Identifying Malicious Activity
- Threat actors, log analysis, Windows logs, firewall logs, DNS logs, proxy logs, email security logs, application logs and NetFlow
- Network behavior anomaly detection, suspicious DNS activity, Tor, peer-to-peer traffic and data loss indicators
- Identifying Patterns of Suspicious Behavior
- Network baselining, anomaly detection, PCAP analysis and suspicious activity investigation with Security Onion
Threat Investigation and Response
- Identifying Resources for Hunting Cyber Threats
- Threat hunting concepts, hunting maturity, hunting cycle, CVSS, threat intelligence sources and threat analytics systems
- Understanding Event Correlation and Normalization
- Event sources, evidence, chain of custody, normalization and event correlation
- Conducting Security Incident Investigations
- Investigation procedures, indicators of compromise, indicators of attack, attribution and advanced threat investigation scenarios
- Using a Playbook Model to Organize Security Monitoring
- Security analytics, playbook structure, playbook management and SOC orchestration
- Describing Incident Response
- Incident response planning, incident response lifecycle, policy elements, incident categories, CSIRT framework and incident handling services
- Security policies, evidence handling, data preservation, volatile data collection, network profiling and server profiling
Attività Laboratoriali
- Configure the Initial Collaboration Lab Environment
- Use NSM Tools to Analyze Data Categories
- Explore Cryptographic Technologies
- Explore TCP/IP Attacks
- Explore Endpoint Security
- Investigate Adversary Methodology
- Hunt Malicious Traffic
- Correlate Event Logs, PCAPs, and Alerts of an Attack
- Investigate Browser-Based Attacks
- Analyze Suspicious DNS Activity
- Explore Security Data for Analysis
- Investigate Suspicious Activity Using Security Onion
- Investigate Advanced Persistent Threats
- Explore SOC Playbooks
- Explore the Windows Operating System
- Explore the Linux Operating System
Tipologia
Corso di Formazione con Docente
Docenti
I docenti sono Istruttori accreditati CISCO e certificati in altre tecnologie IT, con anni di esperienza pratica nel settore e nella Formazione.
Infrastruttura laboratoriale
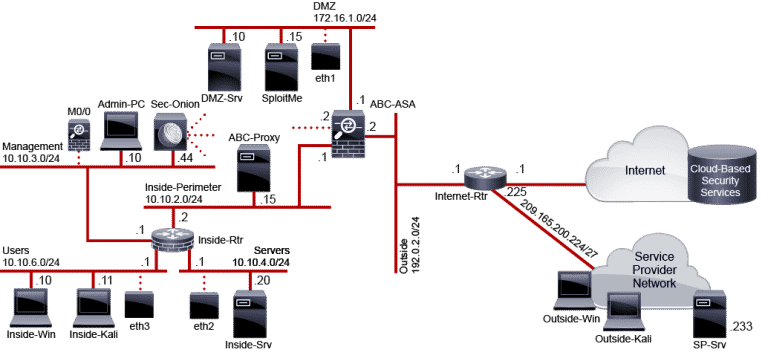
Per tutte le tipologie di erogazione, il Corsista può accedere alle attrezzature e ai sistemi reali Cisco presenti nei Nostri laboratori o direttamente presso i data center Cisco in modalità remota. Ogni partecipante dispone di un accesso per implementare le varie configurazioni avendo così un riscontro pratico e immediato della teoria affrontata. Ecco di seguito alcune topologie di rete dei Laboratori Cisco Disponibili:
Dettagli del corso
Prerequisiti
Nessun Prerequisito.
Durata del corso
- Durata Estensiva 54 Ore;
- Durata Intensiva 5gg;
Frequenza
Varie tipologie di Frequenza Estensiva ed Intensiva.
Date del corso
- Corso CCNA Cybersecurity (Formula Intensiva) – 06/07/2026 – 09:00 – 17:00
Modalità di iscrizione
Le iscrizioni sono a numero chiuso per garantire ai tutti i partecipanti un servizio eccellente.
L’iscrizione avviene richiedendo di essere contattati dal seguente Link, o contattando la sede al numero verde 800-177596 o inviando una richiesta all’email [email protected].

